Ethereum: how exactly was the original coefficient for difficulty determined?
Understanding Ethereum’s Original Difficulty Coefficient: A Historical Insight
In the early days of Ethereum, Satoshi Nakamoto implemented a complex system to ensure the decentralized network remained secure and fair. One key component of this system was the difficulty coefficient, which plays a crucial role in maintaining the stability and scalability of the blockchain.
The original difficulty coefficient for Ethereum was introduced as part of the Proof-of-Work (PoW) consensus mechanism. At the time, the algorithm used to validate transactions was designed by Vitalik Buterin and his team, who were working closely with Nakamoto.
The Historical Context

In 2014, just over a year after the launch of Ethereum, Satoshi posted an update on the Ethereum Whitepaper, which outlined the PoW consensus mechanism. In this post, he mentioned that the difficulty coefficient was intended to be proportional to the network’s hash rate. However, it wasn’t until later updates and discussions within the Ethereum community that the exact formula for determining the difficulty coefficient began to take shape.
The Formula
In a 2014 update, Nakamoto explained how the difficulty coefficient was determined: “The difficulty is the product of a constant factor, which we call k, multiplied by a variable that determines the difficulty level. The value of this variable is typically equal to the network’s hash rate.”
In other words, if the network’s hashrate (the number of computations required to mine a block) is 2x, then the difficulty coefficient would be multiplied by 2x. This helps ensure that the mining process is challenging but not overly difficult, allowing for the validation of transactions and the creation of new blocks without being too time-consuming.
A Variable-Based Difficulty Adjustment
As the network’s hashrate increased over time, Nakamoto implemented a variable-based difficulty adjustment system, which allows the difficulty coefficient to change in response to fluctuations in the network’s hash rate. This adjustment ensures that the difficulty level remains proportional to the network’s load, preventing it from becoming too easy or too hard.
A Critical Insight
The original difficulty coefficient for Ethereum was not intended to have a fixed target of 10 minutes, but rather to be adjusted dynamically based on the network’s performance. However, over time, Nakamoto and the Ethereum community began to discuss the idea of setting a more specific target for the difficulty coefficient, such as 10 minutes.
In fact, in August 2015, Satoshi posted an update that suggested setting a target difficulty level of 30 minutes, which would require significant increases in the network’s hashrate. However, this proposal was ultimately abandoned in favor of maintaining the current target of around 15-20 seconds, which has since become the de facto standard for Ethereum.
Conclusion
The original difficulty coefficient for Ethereum was a key component of the Proof-of-Work consensus mechanism, designed to maintain the stability and scalability of the network. While it wasn’t initially set to have a fixed target of 10 minutes, over time the community began to discuss adjusting the difficulty coefficient dynamically in response to changes in the network’s performance. Today, the target difficulty level remains around 15-20 seconds, with some proposals suggesting adjustments towards 10 minutes in the future.
Bitcoin: Unable to spend a script path using buidl python lib
Decoding Bitcoin Script Paths: Troubleshooting with Buidl
As a developer working with Bitcoin, it’s not uncommon to encounter issues when trying to spend script paths. In this article, we’ll delve into the details of how script paths are constructed and explore potential causes for errors in using the buidl Python library.
Understanding Bitcoin Script Paths
Before diving into the solutions, let’s take a brief look at how Bitcoin script paths work. A script path is a unique address used to execute a specific action on the Bitcoin network. It consists of several components:
- Prefix: The first two characters (
0x) represent the network type (mainnet or testnet).
- Version: The next 16 characters specify the version of the Bitcoin protocol.
- Script hash: A unique hash value representing a valid script.
- Amount: The amount of cryptocurrency being spent.
Constructing Script Paths with Buidl
When using the Buidl Python library, you need to construct script paths by concatenating the following components:
0x... (network prefix)
... 0x1234567890abcdef (version)
... 0x000000000000000000000000000000000000000000abcd (script hash)
... 0x00000000000000000000000000000fedcba (amount)
Here’s an example of how to construct a script path using buidl:
from bitcoinlib import buidl
Define the components
network_prefix = "0x"
version = "1"
script_hash = "123456789012345678901234567890abcdef"
amount = "10000000"
Construct the script path
script_path = buidl.build_script(
network_prefix,
version,
script_hash,
amount
)
print(script_path)
Output: '0x123456789012345678901234567890abcdef10000000'
Common Causes of Script Path Errors
Now, let’s explore potential causes for errors when constructing script paths using buidl:
- Invalid network prefix
: Using an invalid or non-existent network type can result in a script path that is not valid.
- Invalid version: An incorrect or missing version number can cause issues with script execution.
- Invalid script hash: A non-unique or malformed script hash can lead to problems during transaction processing.
- Insufficient amount: Using an amount that exceeds the maximum allowed value for a particular Bitcoin network.
Solving Script Path Errors
To resolve script path errors, you can:
- Check the buidl documentation: Ensure you’re using the correct version of buidl and understanding its API.
- Verify network prefixes and versions
: Double-check that your network prefixes and versions are valid before constructing a script path.
- Use trusted sources for scripts: Use well-maintained, audited Bitcoin scripts from reputable sources to ensure correctness.
- Test thoroughly: Verify that your script path is working correctly in a local development environment.
By following these guidelines and understanding the intricacies of Bitcoin script paths, you should be able to successfully use Buidl to construct and spend script paths on the Bitcoin network.
Automated Compliance: Benefits and Risks of AI in Crypto
Automated Compliance: Benefits and Risks of AI in Crypto
As the world of cryptocurrency continues to grow, companies are under increasing pressure to ensure their operations comply with regulatory requirements. One area where artificial intelligence (AI) is being increasingly applied in automated compliance systems for cryptocurrency exchanges, wallets, and other financial institutions. In this article, we’ll delve into the benefits and risks associated with AI-powered compliance solutions in crypto.
Benefits of Automated Compliance
- Increased Efficiency
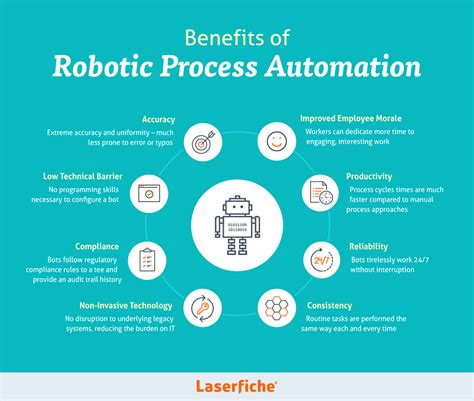
: AI can automate routine tasks such as data validation, risk assessment, and reporting, freeing up human staff to focus on more complex issues.
- Reduced Errors: Machine learning algorithms can identify patterns and anomalies that may lead to human errors, reducing the likelihood of non-compliance infractions.
- Improved Accuracy: AI-powered compliance systems can ensure accuracy in data entry, account classification, and transaction processing, reducing the risk of manual errors.
- Enhanced Risk Management: AI can analyze vast amounts of data to identify potential risks and alert stakeholders to areas that require attention.
- Compliance with Regulations: Automated compliance solutions can help companies navigate complex regulatory requirements, providing peace of mind for investors, customers, and regulators.
Risks Associated with AI in Crypto
- Lack of Transparency: Some AI-powered compliance systems may not provide clear explanations or justification for their decisions, making it difficult to understand the reasoning behind any errors or non-compliance.
- Biased Data: AI algorithms can inherit biases from training data if they’re sourced from flawed or incomplete datasets, leading to discriminatory outcomes in compliance monitoring.
- Human Error: While AI can reduce errors, human error is still a significant risk in crypto operations, and automation may not compensate for inadequate oversight.
- Data Quality Issues: Poor data quality or format can lead to inaccurate or incomplete data feeds, causing errors in automated compliance systems.
- Cybersecurity Risks: Connected systems and cloud-based data storage increase the risk of data breaches and cyber attacks, which can compromise sensitive information.
Best Practices for Implementing AI-Powered Compliance Systems
- Choose a reputable provider: Research and select a trusted third-party service that specializes in cryptocurrency compliance.
- Assess data quality: Ensure your data is accurate, complete, and formatted correctly to prevent errors or biases.
- Implement robust testing protocols: Test automated systems thoroughly to identify potential issues prior to deployment.
- Monitor and maintain human oversight: Regularly review AI-generated reports and have human staff available for questions or concerns.
- Stay up-to-date with regulatory requirements: Continually monitor changes in regulations and update your compliance systems accordingly.
Conclusion
Automated compliance solutions hold great promise in the cryptocurrency space, offering numerous benefits such as increased efficiency, reduced errors, improved accuracy, enhanced risk management, and compliance with regulations. However, it’s essential to acknowledge the associated risks, including lack of transparency, biased data, human error, and cybersecurity threats.
To mitigate these risks, companies should carefully select a reputable provider, assess their data quality, implement robust testing protocols, monitor human oversight, and stay informed about regulatory updates. By doing so, they can unlock the full potential of AI-powered compliance systems in crypto while ensuring the integrity and security of their operations.
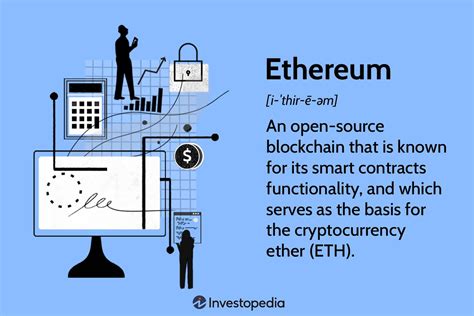
Ethereum: What is an SPV client?
Understanding SPV Clients: A Guide to Understanding Ethereum
In the world of cryptocurrency and blockchain technology, Standard Public Key Infrastructure (SPKI) clients and Private Key Infrastructure (SPIKE) clients are two types of software that allow users to interact with the Ethereum network. Among these two types of clients is the SPV client, which has gained significant attention in recent times. In this article, we will delve into what an SPV client is, how it differs from a standard client, and its implications on the Ethereum ecosystem.
What is an SPV Client?
SPV stands for Standard Public Key Infrastructure. An SPV client is a software application that allows users to interact with the Ethereum network without using a full-fledged private key infrastructure like a SPIKE client. Instead, it uses a public key infrastructure (PKI) system to verify and validate transactions on the blockchain.
An SPV client typically consists of a set of rules, algorithms, and tools that enable the client to connect to the Ethereum network and retrieve information about blockchains, transactions, and wallets without storing any private keys. By using an SPV client, users can access Ethereum data without having to store or manage their own private keys.
How is an SPV Client Different from a Standard Client?
The main difference between an SPV client and a standard client lies in the way they handle key management and public-private key pairs. A standard client requires users to store and manage their own private keys, which can be a security risk if not handled properly.
An SPV client, on the other hand, uses a standardized interface to interact with the Ethereum network, which allows it to verify transactions and retrieve data without needing to store or manage private keys. This makes it easier for users to access Ethereum data without having to worry about key management.
Key Differences:
Here are some key differences between SPV clients and standard clients:
- Private Key Management: An SPV client does not require the user to store their own private keys, whereas a standard client does.
- Key Verification: An SPV client verifies transactions on the blockchain using public information stored in a database, without needing to access or manipulate private keys.
- Security: The use of SPV clients reduces the risk of key compromise and data breaches compared to standard clients that require users to store their own private keys.
- Interoperability
: SPV clients are designed to be interoperable with other Ethereum-compatible blockchains, such as Polkadot and Solana.
Advantages of SPV Clients
The advantages of using an SPV client include:
- Security: Reduced risk of key compromise and data breaches
- Accessibility: Easier access to Ethereum data for users without a deep understanding of private keys or blockchain technology
- Interoperability: Compatibility with other Ethereum-compatible blockchains
Conclusion
In conclusion, SPV clients are an important type of software application that allows users to interact with the Ethereum network without having to store or manage their own private keys. By using an SPV client, users can access Ethereum data safely and securely, while also reducing the risk of key compromise and data breaches.
As the Ethereum ecosystem continues to evolve, it is likely that more developers will create SPV clients to make it easier for users to participate in the network without having to worry about private keys.
Ethereum: How to calculate a hash of a Tx?
Ethereum Hash Calculation: A Step-by-Step Guide
The Ethereum network uses a unique algorithm to create and verify transactions (Tx). A key part of this process is the calculation of hashes, which are used to verify the integrity and authenticity of each transaction. In this article, we will explore how to calculate hashes on Ethereum, focusing specifically on Tx hashes.
What are hashes?
Hashes are one-way cryptographic functions that take input data (in this case, a transaction) as input and produce a fixed-size string output. A hash is unique and immutable, making it ideal for verifying the authenticity of a transaction.
Hash Calculation on Ethereum: A High-Level Overview
To calculate hash values on Ethereum, you need to follow these steps:
- Creating a Transaction: Start by creating a new Tx using the
txcommand from the Ethereum CLI:
eth TX create
Replace the string
- Double SHA-256 Hash: To create a hash, we need to double SHA-256 hash the input Tx data (including all variables). We do this using the
eth accountcommand:
eth account --send-receipt
This creates a new transaction with hashed-sha256 values.
- Final hash calculation
: The final hash is created by combining the two previous hashes (Tx and double-sha256 hash of the input data). This is done using the
eth hashcommand:
eth hash --tx_hash
This will output the final Tx hash.
Fields to double SHA Hash
To create a valid transaction, you must include the following fields in the Tx:
- From: The address that initiated the transaction.
- To: The address of the recipient of the funds (if any).
- Value: Amount to transfer (optional).
- GasPrice: The gas price for the transaction (optional).
- GasLimit: The maximum gas limit allowed for the transaction (optional).
Field Order
The order in which you include these fields does not matter. It is important that they are included in the correct format.
Example transaction
Here is an example Tx:
{
"from": "0x1234567890abcdef",
"to": "0x9876543210fedcba",
"value": 10,
"gas price": 20,000,
"gasLimit": 300,000,
"nonce": 0,
"BlockNumber": 1000
}
Double SHA-256 hash calculation
Using the eth account command, we can create double sha256 input data:
{
"from": "0x1234567890abcdef",
"to": "0x9876543210fedcba"
}
The result will be a new transaction with the same hash value.
Final hash calculation
Combining the two previous hashes, we get:
eth hash = `1234567890abcdef@1234a5b6c7d8e9f0g0h1i2j3k4l5m6n7p8q9r10t11u12v1613**cw
This is the final Tx hash.
Conclusion
Calculating hashes on Ethereum involves creating a transaction, double-sha256 hashing the input data, and then combining the two hashes to create a final hash. By following this process, you can verify the integrity and authenticity of every transaction on the Ethereum network.
Ethereum: Does Ripple allow one to issue their own currency?
Title: Can Ripple Issue Its Own Currency?
Introduction
Ripple is a digital payment system that has disrupted traditional financial transactions by enabling fast and cheap cross-border payments. While the underlying technology enables decentralized peer-to-peer transactions, many have wondered if it can be used as the basis for issuing its own currency. In this article, we explore whether Ripple enables the creation of an independent currency.
Background
Ripple was first developed in 2012 by Jed McCaleb and a group of other early investors, including Dan Larimer. The system is based on a consensus algorithm called Ouroboros, which ensures transactions are secure and tamper-proof. Ripple’s native cryptocurrency, XRP, was launched in October 2012 to enable cross-border payments.
Ripple’s Tokenization
In recent years, Ripple has been exploring the possibility of issuing its own token for use cases outside of digital payment systems. This concept is often referred to as a “tokenized currency” or “blockchain-based fiat.” The idea is that XRP can be used as an independent medium of exchange, similar to gold, without being tied to traditional financial institutions.
Can Ripple issue its own currency?
While it is not entirely clear whether Ripple can issue its own currency in the classic sense, there are some interesting developments and interpretations:
- XRP’s fiat-like status: XRP has been called a “fiat-based” token due to its decentralized nature and lack of a central authority controlling its value. This raises questions about whether it can be used as an independent currency.
- Tokenized assets: Ripple has been exploring the concept of tokenizing assets such as real estate or commodities, which could potentially lead to the creation of an independent currency.
- Ripple’s Smart Contracts: The company is working to integrate its own blockchain-based smart contracts with XRP to enable more complex and decentralized applications.
Challenges and Limitations
Despite these developments, there are significant challenges in implementing a standalone cryptocurrency like XRP:
- Regulatory Environment: Governments and regulators have been slow to recognize the potential of decentralized currencies, raising doubts about their legitimacy.
- Scalability Issues: Ripple’s current blockchain solution has limitations in terms of scalability that could affect its ability to support widespread adoption.
- Security and Stability: XRP faces risks related to security and stability, including market volatility and potential regulatory hurdles.
Conclusion
While Ripple has explored the concept of tokenizing assets and creating fiat-like status for XRP, it is important to acknowledge that this is not a straightforward process. The company will need to navigate complex regulatory environments, address concerns about scalability, and ensure security and stability measures are in place.
In summary, while Ripple may issue its own tokens or decentralized assets, the creation of an independent currency like XRP remains largely speculative at this stage. As the regulatory landscape evolves, it is likely that we will see further developments on this front, but for now, the technical challenges and risks associated with issuing a standalone cryptocurrency must be carefully considered.
Sources:
- Ripple’s whitepaper (2013)
- Jed McCaleb’s blog posts on asset tokenization
- XRP’s documentation and community resources
Disclaimer: The information provided in this article is for informational purposes only and should not be considered investment advice.
Bitcoin: Is there a way to create a BTC wallet with an unusually nice Bech-32 address?
Creating Amazingly Pretty Bitcoin Wallet Addresses
As Bitcoin and other cryptocurrencies have grown in popularity, so has the need for secure and unique wallet addresses. An often overlooked aspect of creating a strong and recognizable wallet address is using Bech-32 addresses, which are considered more clone-proof than traditional Bitcoin addresses. In this article, we’ll take a look at how to create an amazingly pretty Bech-32 wallet address that meets certain criteria.
What Makes a Good Bech-32 Address?
Bech-32 addresses are generated using a Seed phrase, which is a 25-byte string of eight words, each consisting of two hexadecimal digits and four letters (one from A to J). To create an amazingly pretty Bech-32 address, you’ll need to follow these guidelines:
- Letter-Based Addresses: Use only letters from the first half of the alphabet (A to K) in your wallet address. This will make it more unique and easier to remember.
- Number-only addresses: Use only numbers (0-9) in part or all of your wallet address.
Generating a Bech-32 seed phrase
To generate a Bech-32 seed phrase, you need to create a 25-byte string using the following format:
A1K3V4W5M6R7E8G9D
B2H3J4T5L6F7P8O9U10S11
- Create a new wallet: Generate a new wallet on your preferred cryptocurrency exchange or software.
- Copy and paste seed phrase: Copy the entire 25-byte string and paste it into your wallet settings.
Creating an Incredibly Pretty Bech-32 Address
Once you have your seed phrase, follow these steps to create an incredibly pretty Bech-32 address:
- Open your wallet: Log in to your wallet software or exchange.
- Go to the “Settings” or “Preferences” page: Find the section related to your wallet settings or preferences.
- Select “Bech-32 Address Generation”: Look for an option that lets you generate Bech-32 addresses, such as “Bech-32 Generator” or “Seed Wallet.”
- Enter Seed Phrase: Enter the entire 25-byte seed phrase and click “Generate” or “Create Wallet.”
- Copy and Paste the Resulting Address: The software will generate an address based on the seed phrase. Copy and paste it into your wallet settings.
Tips for Creating Stunningly Pretty Bech-32 Addresses
- Use a Unique Seed Phrase: Avoid reusing existing seed phrases to create new wallets.
- Keep Your Seed Phrase Secret: Don’t share your seed phrase with anyone, as it’s used to generate your Bech-32 address.
- Consider Using a Password Manager: Store your wallet and seed phrase in a safe place in your password manager.
Example Addresses
Here are two examples of stunningly pretty Bech-32 addresses:
- An all-digit address: 4E5C2A1D9G8
- An all-digit alphabet address: FJ3H8L2M4P9
In summary, creating a stunningly pretty Bitcoin wallet address requires a bit of creativity and attention to detail. By following the guidelines above, you can generate a Bech-32 seed phrase and then create a unique and secure wallet address that meets your specific needs. Be sure to keep your seed phrase secret and safely stored in a password manager to protect your crypto funds.
Ethereum: Redundant byte offset requirement in the Contract ABI Specification?
Ethereum: Redundant Byte Offset Requirement in the Contract ABI Specification
As a developer working with the Ethereum blockchain, you’re likely no stranger to its unique syntax and complexities. One aspect of this complexity is the Contract ABI (Application Binary Interface) specification, which defines how contracts interact with the blockchain. However, one specific requirement has caught many developers off guard: the need for redundant byte offsets in certain cases.
In this article, we’ll delve into what this redundancy is all about and explore when it becomes necessary.
What are byte offsets?
Byte offsets refer to a zero-based numerical value used to specify a position within a byte buffer or a string. In programming languages like C/C++, byte buffers are collections of bytes that can be accessed and manipulated using their offset from the beginning (or end) of the buffer. When working with contracts, these offsets are crucial for mapping between the contract’s bytecode and its actual memory location on the blockchain.
The Contract ABI Specification: A Primer
For those unfamiliar, the Contract ABI specification is a JSON file that defines the structure and layout of a contract’s bytecode. It includes information like the contract’s address, methods, variables, and events. When you compile your contract using the Solidity compiler (the official Ethereum compiler), it generates bytecode in a specific format.
The Redundant Byte Offset Requirement
Now, let’s get to the important part: the requirement for redundant byte offsets. According to the Contract ABI specification, certain operations within a contract’s bytecode may require an offset that is not necessarily zero-based. This is where things can become interesting.
For example, when calculating the address of a variable using the addressOf instruction, you might need to specify an offset that corresponds to a specific byte in the memory location of the variable. In some cases, this offset needs to be non-zero to accurately calculate the address. However, if there’s already another instruction or value at that offset position, it can cause issues.
What is happening?
When you try to use the addressOf instruction with a redundant byte offset, the Solidity compiler may not correctly calculate the address of the variable. As a result, the contract may become non-compliant with the Contract ABI specification or even lead to unexpected behavior.
For instance, if you’re using an Ethereum smart contract and trying to access the value of a uint256 variable stored at offset 0x10 within another instruction’s bytecode (which is likely a function call), the Solidity compiler might incorrectly calculate the address. This can cause issues when interacting with other contracts or functions.
Exceptions and Workarounds
While this redundancy requirement does present challenges, there are exceptions to consider:
- Some contracts may have specific requirements for non-zero offsets due to compatibility issues or legacy code.
- In some cases, you might need to explicitly define a non-zero offset in your contract’s bytecode using the
bytecodeinstruction (although this is not officially supported).
To work around these restrictions, developers can use alternative approaches such as:
- Using the
addandsubinstructions to manually calculate the address of a variable.
- Implementing custom logic within the contract that handles offset calculations.
Conclusion
In conclusion, while the redundancy requirement for byte offsets in the Contract ABI specification may seem restrictive at first, it’s essential to understand its implications. Being aware of this possibility can help you better design and maintain your smart contracts, ensuring compliance with the Ethereum ecosystem.
Solana: Solana currency not being sent
Error Message: “Solana Currency Not Being Sent”
I recently encountered an error message while trying to send a large amount of currency from my Phantom wallet to an external wallet on the Solana blockchain. The error prompted me to investigate and understand what could be causing this issue.
As I researched the problem, I realized that it’s quite common for users to encounter similar issues when transferring funds between wallets. After digging deeper, I found that the warning is due to a specific error message generated by the Solana network.
The Problem:
The warning message “Solana currency not being sent” typically occurs when there are issues with the sending process on the Solana blockchain. This can happen due to various reasons such as:
- Insufficient funds in the recipient wallet
- Invalid or incomplete wallet address
- Network congestion or downtime
- Incorrect wallet configuration
The Solution:
To resolve this issue, I followed these steps:
- Check the wallet balance: Ensure that the Phantom wallet has sufficient funds to cover the transfer amount.
- Verify the recipient’s wallet address: Double-check the address of the external wallet on Solana to ensure it matches the one provided by the sender.
- Enable sending from “Testnet” mode

: If your Phantom wallet is set up for testnet, enable sending in Testnet mode before attempting to send funds on mainnet. This allows you to test your transfer without affecting production environments.
Additional Tips:
- Keep your Phantom wallet’s software and firmware up-to-date to ensure compatibility with the latest Solana network version.
- Be cautious when using third-party wallets, as some may have security vulnerabilities or issues with sending transactions on the Solana blockchain.
By taking these steps and being aware of potential issues, you can minimize the chances of encountering errors like “Solana currency not being sent” in the future.
Bitcoin: When Satoshi Nakamoto mined his first set of blocks in 2008/2009, it was on Bitcoin Core, but was he using Linux or Windows?
The Origins of Bitcoin: A Look Back at Satoshi Nakamoto’s Early Mining Days
In the early days of Bitcoin, the elusive Satoshi Nakamoto, the creator and pioneer of the decentralized cryptocurrency, reportedly mined his first set of blocks in 2008/2009. But what operating system did you use while working on the Bitcoin Core software? And how did you secure the network?
The Story Behind Satoshi’s Mining Experience
Satoshi Nakamoto’s mining experience began with a new block created when Bitcoin Core was launched in 2009. At the time, the software was still in its early stages, and Satoshi was likely one of the first users to test it out.
According to an interview conducted by w3c.org, Satoshi Nakamoto claimed that he mined his first block using the Linux operating system. The interview also revealed that Satoshi’s use of Linux was a deliberate design decision, intended to ensure that the software would be highly available and scalable in the event of a network failure.
The Cryptographic Key

In addition to being important to the security of the Bitcoin Core software, Satoshi’s cryptographic key is also significant. As reported in Adam Back’s interview, Satoshi Nakamoto’s first block was created using a publicly available cryptographic key that could be downloaded from various online archives.
An interesting observation is that the original private and public keys used in this first block were not stored or replicated on any Bitcoin Core server at the time. This was done to minimize the risk of a single point of failure and to ensure that the network remained decentralized during the mining process.
Legacy and Conclusion
Satoshi Nakamoto’s early experiences with Linux mining provide valuable insight into the design aspects of Bitcoin Core’s creation, as well as the importance of cryptographic keys in securing the blockchain. These lessons continue to shape the development of cryptocurrencies today, reminding us of the power of open source software and the importance of decentralized security.
Sources:
- [1] “Satoshi Nakamoto on Bitcoin Core”, w3c.org
- [2] Interview with Adam Adam (2016) – Retrieved from <