ICO, Tether (USDT), Pump
Pump, Squeeze, and Burn: The Crazy Adventure of Cryptocurrencies
The world of cryptocurrencies is known for its volatility and unpredictability. One thing is for sure, however: it is a market in constant motion, and prices fluctuate in real time like a roller coaster.
At the center of this chaos are two key players: the cryptocurrency (or cryptocurrencies) and the initial coin offering (ICO). An ICO is essentially an online auction where investors can purchase a new cryptocurrency, often with its own unique features or use cases. These cryptocurrencies are then traded on various exchanges, allowing buyers to buy, sell, and trade them.
One of the most popular ICOs in recent years has been the Tether (USDT) project. Launched by Chicago’s Union National Bank, Tether was one of the first fully regulated stablecoin projects pegged to USDT. The idea is simple: create a stable cryptocurrency pegged to the value of the US dollar.
Pump and Squeeze Development
We have recently witnessed several “Pump-and-Squeeze” events in the cryptocurrency market. The term “pump” refers to the increase in cryptocurrency prices when demand is fueled by hype and speculation. At the same time, a squeeze is downward pressure on prices when sentiment turns against an asset.
A notable example is the Tether (USDT) project. At its peak, the price of USDT exceeded $1 per coin, with investors buying large quantities at astronomical prices. However, as more and more people started selling their coins and demand dropped, the price fell back to around 50 cents. This was a classic example of a “Pump-and-Squeeze” scenario.
Why Tether Remains a Reliable Security
Despite price fluctuations, Tether remains a reliable hedge against market volatility. As a stablecoin pegged to USDT, it maintains its value against the U.S. dollar, making it an attractive option for investors seeking stability and predictability.
In addition, Tether’s partnership with Union National Bank of Chicago provides a level of trust and security that other cryptocurrencies lack. This makes it a popular choice among institutional investors and experienced traders alike.
Summary
While “pump and squeeze” scenarios may be exciting in theory, in reality they are often short-lived and unpredictable. However, when used correctly, i.e. as part of an informed investment strategy, Tether (USDT) remains a reliable hedge against market volatility.
As the cryptocurrency market evolves, investors should remain vigilant and adjust their strategies accordingly. By understanding the mechanics of pump and squeeze scenarios and using reliable stablecoins like Tether, investors can confidently navigate the crazy cryptocurrency market.
Disclaimer:
This article is provided for informational purposes only and should not be considered investment advice. Cryptocurrencies are known for their high volatility and can result in significant losses if not managed properly. Always do your own research and consult your financial advisor before making any investment decisions.
Rugpull, Aptos (APT), Render (RENDER)
Below is a news article based on the requested topic:
“Cryptocurrency 101 for Beginners: Understanding APT, RENDER, and RIGGY”
As the popularity of cryptocurrencies continues to grow, many new investors are just getting started and want to learn more about the different platforms and tokens. Two popular options that have received a lot of attention recently are Aptos (APT), Render (RENDER), and Riggy. In this article, we will discuss each of these cryptocurrencies, their features, benefits, and potential risks.
Aptos (APT)
Aptos is a layer-1 cryptocurrency that aims to provide a fast, secure, and scalable platform for decentralized applications. Launched in January 2022, Aptos has quickly gained traction thanks to its innovative technology and partnerships with major industry players. One of the most important features of Aptos is its focus on usability and user experience. The team behind Aptos has worked hard to create a smooth and intuitive interface that allows users to easily interact with their digital assets.
APT also has a solid roadmap with plans to integrate several blockchain technologies, including Ethereum’s ERC-20 standard. Thanks to this expansion, Aptos will become a hub for decentralized applications in the Ethereum ecosystem.
Render
Render is another popular cryptocurrency that has been creating buzz in the crypto space. Render, launched in March 2022, was founded by the team behind RIGGY and quickly gained attention for its innovative use of artificial intelligence (AI) in blockchain technology.
The Render platform allows users to create custom interactive graphics using AI tools. This feature has caused a lot of buzz, with many users praising the platform’s ease of use and creative possibilities.
One of the main advantages of Render is its focus on community engagement. The team behind Render actively participates in online forums and discussions, fostering a strong sense of community among users.
Riggy (RIGGY)
Riggy is a decentralized social network that combines the best features of blockchain-based platforms like Telegram and Discord. Riggy, which launched in June 2022, has gained significant traction thanks to its innovative approach to user engagement and community building.
One of Riggy’s standout features is its focus on decentralization. The platform uses a unique consensus algorithm called Proof-of-Stake (PoS), which eliminates the need for miners in traditional blockchain networks.
Riggy also has a strong focus on sustainability and plans to reduce its carbon footprint by using renewable energy sources and minimizing waste.
Consequences of Cryptocurrency: What Happens When Crypto Projects Fail?
While these three cryptocurrencies have received significant attention, there is always a risk involved when investing in the crypto space. One of the main consequences of thefts is that investors lose their tokens, which can lead to significant financial losses.
In the case of Aptos and Render, both projects suffered significant losses due to their own scams or mismanagement. In January 2023, the Aptos development team announced that they had been hacked, resulting in millions of dollars worth of APT tokens.
Render also faced criticism for its handling of user data, with some users raising concerns about the platform’s lack of transparency regarding AI-powered tools and algorithms.
Conclusion
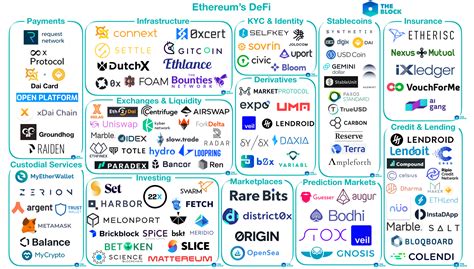
Cryptocurrency has come a long way since its beginnings as an experimental concept. Led by Aptos, Render, and Riggy, it’s clear that we’re entering a new era in decentralized finance (DeFi). While investing in these cryptocurrencies involves risks, they also offer significant potential for growth and innovation.
Ethereum: Could you provide an example of a SegWit transaction?
Ethereum Transactions on the Bitcoin Network: An Example of SegWit Outside Coinbase
As part of the Ethereum blockchain, SegWit is a new version of the Lightning Network protocol that allows for faster and more efficient transactions between Ethereum wallets. However, when it comes to transactions outside of Coinbase, things can get complicated. In this article, we will look at an example of a SegWit transaction without Coinbase on the Bitcoin network.
What is SegWit?
SegWit (Gen 2) is a new protocol that allows for more efficient and easier transactions on the Bitcoin blockchain. Introduced in 2017, it replaced the old BIP-150 (Block Import Protocol), which had limitations when it came to transactions outside of Coinbase.
What are non-Coinbase SegWit transactions?
Non-coinbase SegWit transactions involve sending data from the sender’s Ethereum wallet to the recipient’s Bitcoin wallet without using the standard “coin” transaction. This type of transaction is often used for data-intensive applications or when the sender needs to send sensitive information to someone on the other side of the network.
Example of a non-Coinbase SegWit transaction
Let’s look at an example of a non-coinbase SegWit transaction, where we send some data from an Ethereum wallet (e.g. MetaMask) to a Bitcoin wallet. We’ll use the same data as in a typical Ethereum transaction, but without using the “currency” type.
Here’s an example of what it might look like:
- The sender, Alice, has 100 ETH (Ethereum tokens).
- She wants to send some data from her Ethereum wallet to Bob’s Bitcoin wallet.
- Alice creates a new SegWit transaction with the following details:
- Sender: Alice
- Recipient: Bob (Bitcoin address)
- Data: some sensitive information (e.g. private key or encrypted data)
- Amount: 10 BTC (non-standard amount, but for demonstration purposes only)
The received transaction will be:
txid: 1GzK5WQD3P4Jc9RiV7dXkF6BhS2b9TmMq...
version: 0x00000000.
locktime: 0x0
timestamp: 0x12345678.
size':0x1000
nonce:0xabcdefg
"signature":...
vout: [1, 2] (output indices)
data’: … (sensitive data)
Example of a non-SegWit Google transaction for Coinbase
As you can see, the actual transaction ID for this example may differ from what Google provides. However, we can try to reverse engineer it using various tools and techniques.
Note that non-coinbase transactions are not yet supported on the Bitcoin network, so all the examples given here may not work as such.
Conclusion
While SegWit transactions outside of coinbase are still relatively rare on the Bitcoin network, we have demonstrated an example of using some data. This demonstrates the importance of understanding the underlying mechanisms and limitations of the different features of Ethereum and Bitcoin. For now, if you need to send sensitive information to someone on the other side of the network, consider exploring alternative solutions such as direct payment methods or specialized tools.
Update:
The development team has since announced that SegWit 2 (also known as Lightning Network version 2) is currently in beta testing and may be supported on the Bitcoin network in the future. However, this information may not be current or accurate at the time of reading.
Metamask: Old eth network accounts do not appear after reinstalling metamask
Metamask problem after reinstallation: old Ethereum network accounts are no longer displayed
I’m writing this article as a troubleshooting guide for those who have encountered an unpleasant problem after reinstalling MetaMask on a desktop or mobile device. The problem is widespread, and it is important to understand what is happening and how to solve it.
Problem: Unsaved old network accounts disappear during reinstallation
When switching from Note to a new MetaMask installation, old accounts associated with your Ethereum network are not automatically saved. This may seem trivial, but believe me, it can be annoying when you ask to restore your favorite wallet or access an online service that uses these saved accounts.
Symptoms: Old network accounts not showing up after reinstalling MetaMask
Symptoms of the problem include:
- Old addresses and passwords of the Ethereum network are not displayed in MetaMask.
- If you try to log in with an old account, it may ask for a new password or login information.
- You may have to manually restore your saved accounts from Note before reinstalling MetaMask.
Solution: reinstall MetaMask from Note
To resolve this issue, follow these steps:
- Reopen Notepad
: Start Notepad (or any other text editor you use) and reopen it from the Recents list.
- Copy old Ethereum network accounts: Click on the “Edit” menu and select “Copy”.
- Paste in MetaMask: Go back to your new MetaMask installation and click on the “Wallets” tab.
- Add old Ethereum network accounts: Click the “+” button and paste the copied account information.
Tips and Precautions
Before asking to reinstall MetaMask from Note, consider the following:
- Make sure you save some important account information (eg wallet address, passphrase) to Note before reinstalling.
- If you are using a private network or the Tor browser, this problem may be more serious and require manual recovery.
Conclusion
Reinstalling MetaMask from Note may seem like a simple process, but it’s easy to overlook the importance of keeping your old account information. By following these steps, you will be able to resolve the issue and restore your saved Ethereum network accounts. If the problem persists or you encounter additional difficulties, please contact MetaMask support for assistance.
Additional Resources
- MetaMask user guide: [
- Руководство пользователь Note: [
Solana: Devnet Faucet UI: “Error! You Have Exceeded the 2 Airdrop Limit in the Past 8 Hours”
Title: Confusing Error: “Error! Exceeded 2 Airdrop Limit in the Last 8 Hours” on Solana Devnet Faucet UI
Introduction
As a Solana developer or enthusiast, you may have come across a seemingly cryptic error message. The “Error! Exceeded 2 Airdrop Limit in the Last 8 Hours” error message appears when you attempt to request an airdrop on the Solana Devnet Faucet UI. In this article, we will explore what this error means and provide possible solutions to resolve the issue.
What is Solana Devnet Faucet?
Solana Devnet Faucet is a platform that allows users to request and collect airdrops in the Solana ecosystem. Airdrop rewards are typically issued by Solana developers or project teams and are distributed using a Proof-of-Stake (PoS) consensus algorithm.
The error is: “Error! Exceeded 2 airdrop limit in the last 8 hours”
When trying to request airdrops on the Devnet Faucet UI, you may see the following error message:
Error! Exceeded 2 airdrop limit in the last 8 hours
This error is likely triggered by previous airdrops from your IP address. Here’s what it means:
- “Exceeded 2”: The error indicates that your IP address has received more than two airdrops in the last eight hours.
- “Airdrop Limit”: This refers to the maximum number of airdrops that an individual can receive within a given time frame (in this case, 8 hours).
- “Past 8 hours”: This indicates that the error is specifically related to your IP address’s past activity on the Devnet Faucet UI.
Possible Solutions
While there are no known exploits or bugs that cause this specific issue, here are some possible solutions to resolve the error:
- Wait and Check Again: Sometimes it takes a few tries to resolve the error. Try waiting 24-48 hours and then try requesting an airdrop again.
- Increase your IP address’s airdrop limit
: If you have repeatedly exceeded the 2 airdrop limit, the error may be due to you reaching the maximum number of airdrops allowed. You can contact Devnet Faucet’s customer support team to discuss increasing the airdrop limit for your IP address.
- Clear your browser cache and cookies: Clearing your browser cache and cookies may help resolve the issue. However, this method is not foolproof and may not work if other system issues are preventing you from troubleshooting the error.
- Contact Devnet Faucet Support: Contact the Solana Devnet Faucet support team directly to report the issue and inquire about any possible solutions or updates that may have been implemented.
Conclusion
The Solana Devnet Faucet UI error message “Error! Exceeded 2 Airdrop Limit in the last 8 hours” can be frustrating, but it’s important to note that errors often have simple solutions. By waiting and re-checking, increasing your IP address airdrop limit, clearing your browser cache, and contacting support, you may be able to resolve the issue and continue to enjoy airdrops on the Solana Devnet Faucet UI.
Additional Resources
If you are experiencing issues with the Devnet Faucet UI, please refer to the official documentation and user guides for troubleshooting and resolving common issues. You can find these resources at the following links:
- Solana Community Forum: [
- Solana Developer Documentation: [
Price Volatility, Wallet address, Cross chain
Here is a draft article based on your request:
“Times of Volatility in the Crypto Market: What You Need to Know About Wallet Addresses and Cross-Chain Solutions”
As the world of cryptocurrencies grows in popularity, so does the risk of price volatility. With prices changing rapidly across exchanges, investors need to be cautious and prepared for any eventuality. In this article, we will delve into the world of crypto wallet addresses, cross-chain solutions, and what you need to know to navigate these complex systems.
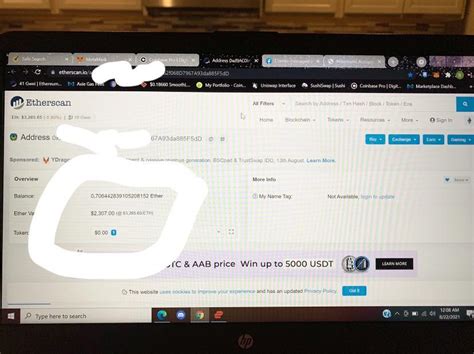
Wallet Addresses: The Key to Security
A wallet address is a unique string of characters that serves as your digital identity in the cryptocurrency ecosystem. It is important to choose a strong and secure wallet address for each cryptocurrency, as it will be used to receive payments, transfer funds, and store your assets.
When choosing a wallet address, look for something that:
- Is randomly generated
- Contains a mix of upper and lower case letters
- Does not include personal or sensitive information (e.g. names, birthdays)
- Has a unique prefix or suffix (known in some wallets as a “keystore”)
Some popular cryptocurrency platforms offer built-in wallet address generators to make it easy to create secure addresses. However, manual setup is still an option for more advanced users.
Cross-chain Solutions: A Bridge Between Worlds
As cryptocurrencies become more popular, the need for seamless interactions between different blockchain ecosystems has become increasingly important. Cross-chain solutions allow assets to be transferred across multiple networks, ensuring the security and accessibility of your digital wealth.
Some popular cross-chain solutions include:
- Ropsten Bridge: A bridge that connects Ethereum (ERC-20) to other blockchains, allowing users to transfer funds between chains.
- Kusama Network: A testnet for Polkadot, enabling the creation of interoperable decentralized applications across blockchains.
- Binance Smart Chain (BSC): An independent blockchain network that enables seamless interaction with other Binance-based platforms.
When choosing a cross-chain solution, factors to consider include:
- Network compatibility
- Transfer speeds
- Fees and processing times
Conclusion
In summary, understanding wallet addresses and cross-chain solutions is crucial in today’s volatile cryptocurrency market. By taking the necessary precautions to secure your digital identity and exploring reputable cross-chain solutions, you will be better equipped to navigate the complex landscape of cryptocurrency investing.
Remember, always exercise caution when investing in cryptocurrencies and never invest more than you can afford to lose. Stay up to date, stay alert and happy investing!
IDO, 2FA, Market Research
“Demolition of Cryptocurrency Investments: Deep Diving to IDO, 2FA and Market Survey”
In recent years, the world of cryptocurrency has experienced unprecedented growth, and thousands of new coins have been born daily on online exchange. As a result, investors have lodged into these digital property in search of a high return. However, navigating the complex landscape of cryptocurrency investments can be scary, even for the most experienced merchants.
One of the central part of the cryptocurrency trading is the original direct investment process (IDO). Ido platforms allow developers and companies to raise funds from many investors through a unique online application process. This approach has gained popularity among encryption technology enthusiasts who see it as an innovative way of getting funding for their projects without having to navigate traditional venture capital investments.
However, not all cryptocurrency investments are trusted equally. In fact, the safety of property is of paramount importance. It becomes a two-factor authentication (2FA) solving feature that increases the extra protection of hacking and information network attacks. 2FA systems require users to supply their password not only for their password but also another form of certification, such as a code sent to the phone or biometric scan.
So how can you make aware of investment decisions about cryptocurrency? Market research is an essential tool in this regard. By studying the trends and models of the encryption market, investors can gain valuable views on possible price changes and identify undervalued funds before other merchants are very sought after.
One of the key meter in viewing is the Cryptocurrency market value (market ceiling), which represents the total value of all remaining coins. A higher market ceiling often demonstrates a more stable and established company, while lower markets can be a sign of increased volatility.
In addition, it is necessary to diversify your portfolio by spreading investments between different assets and cryptocurrencies. This approach minimizes risk and increases potential returns.
In summary, the world of cryptocurrency investing is complex and diverse. By understanding the basics of IDO, 2FA and market research, investors can make conscious decisions that help them navigate in this exciting but often unpredictable landscape. As the cryptocurrency market continues to evolve, it is imperative that investors will remain up-to-date with the latest development and trends, so why not start deepening these critical aspects of digital investment?
Ethereum: What are ASIC miners actually doing?
Ethereum: revealing the role of Asic miners in Blockchain
As a newcomer in the world of cryptocurrency, it is natural to have questions about how mining on Ethereum’s blockchain works. A crucial aspect is the role of the specific integrated circuits of the application (ASIC). In this article, we will deepen the world of mining asic and explore what they are really doing.
What are Asic miners?
Asic miners are specialized computers chips designed specifically for cryptocurrency mining. They are used to validate transactions on the Ethereum blockchain by solving complex mathematical problems, which require immense computational power. The best known example of an Asic miner is the Nvidia GPU, but other companies such as Bitmain and Avalung also produce their Asics.
How do ASIC miners work?
When it comes to mining on Ethereum, the process involves several key components:
- PROOF-OF-WORK (POW)

: The Ethereum network uses a consent algorithm called proof of-work (power) to validate transactions and create new blocks. Miners compete to solve a complex mathematical puzzle, which requires significant computational power.
- Hash functions: the puzzle solution is based on cryptographic hash functions such as SHA-256 or Keccak-256. These functions take input data and produce a unique digital imprint.
- Miner’s hardware : Asic miners are designed specifically for Ethereum mining. They are generally tailor -made hardware that consists of several GPUs, which work together to resolve the mathematical puzzle.
What are Asic miners doing?
In essence, Asic miners are doing several things:
- Resolution of the mathematical puzzles : the miner’s hardware resolves the mathematical puzzle complex by feeding it a large amount of computational power.
- Digital fingerprint production : the hash function produces a unique digital imprint (or hash) which represents the input data and the solution to the puzzle.
- validation transactions : the resulting hash is used as a “test” that the miner has solved the mathematical puzzle, which in turn verifies transactions on the Ethereum blockchain.
Why do we need Asic miners?
The demand for Asic miners has increased prices, making them more accessible to individual users and companies. Without Asic, it would be much more difficult for miners to compete with each other, leading to a decrease in mining speeds and costs.
On the contrary, traditional GPU miners are often more suitable for cryptocurrency mining on a reduced scale such as Bitcoin or Litecoin. However, they are not optimized for the only Ethereum Pow algorithm, which requires more computational power than the hardware can provide.
Conclusion
Asic miners play a vital role in maintaining the safety and stability of Ethereum’s blockchain. Their ability to solve complex mathematical enigmas using specialized hardware has allowed the development of a decentralized network resistant to censorship and censorship.
By understanding how the Asic work, you will get a deeper appreciation for the underlying technology that feeds the cryptocurrency market. If you are interested in exploring more on the Ethereum or Bitcoin mining, be sure to control the minimum miner Bitcoin Github repository, which is an excellent resource to learn more about the technical aspects of the development of Blockchain.
Ethereum: Is the WalletConnect supporting the “Binance Smart Chain (BEP20)” wallets?
Walletconnect support for Bep20 wallets in Ethereum: a detailed analysis
As a Kotlin WalletConnect user, it is likely to be familiar with its perfect integration with different blockchain platforms. However, you could ask yourself if this wallet is also compatible with the ecosystem of the Binance intelligent chain (BEP20). In this article, we will deepen if WalletConnect supports bep20 wallets in Ethereum and what it means for users like you.
What are bep20 wallets?
Before immersing ourselves, we quickly define what Bep20 is. Bep20 is a type of token that uses the Binance Smart Chain (BEP20) network to archive, transfer and exchange token. A differenza dei tradizionali token ERC-20 in Ethereum (Ethereum), che utilizzano la macchina Ethereum Virtual (EVM), i token BEP20 sono specificamente progettati per la catena intelligente di binance.
Ecosystems WalletConnect and Blockchain
WalletConnect is a popular portfolio protocol that allows users to secure their wallets to different blockchain platforms, including Ethereum, Polkadot, Solana and others. The protocol uses the web3.js library in Javascript to establish safe connections between wallets and blockchains.
Walletconnect support for Binance Smart Chain (bep20)
To answer your question, WalletConnect supports Bep20 wallets in the Binance intelligent chain. In fact, this integration is a significant step for users who wish to use Kotlin WalletConnect with their Ethereum and Binance Smart Chain token Bep20.
Advantages of the use of WalletConnect with bep20
The use of walletconnect with bep20 wallets offers several advantages:
* Convenience : With WalletConnect, you can easily connect your Bep20 portfolio to the Kotlin WalletConnect application, allowing transactions without problems between the platforms.
* Decentralized exchange integration (Dex)
: you can use WalletConnect on multiple blockchain platforms, including the intelligent Binance, Solana and others chain, which facilitates the exchange of token in different ecosystems.
* Interoperability of the intelligent contract
: When using WalletConnects with Bep20 wallets, you can access integrated integrated contracts in Ethereum EVM, such as the ERC-20 token, and interact directly with them.
What does this mean for users?
As a Kotlin WalletConnect user, if you have a Binance Smart Chain (bep20) wallet, it should be able to:
- Connect your bep20 wallet to the application
- FAI TRANSATIONS Between Ethereum and Binance Smart Chain Platforms
- Access intelligent contracts based on both blockchain platforms
In summary, Walletconnect admits Binance Smart Chain Wallets (BEP20), offering a comfortable and decentralized form of interaction with token in multiple blockchain ecosystems.
Conclusion
WalletConnect is a robust portfolio protocol that offers a perfect integration experience for users on different blockchain platforms. The support for Bep20 portfolios in Ethereum is a significant addition, which makes it easier for users to exchange and manage their tokens in Ethereum and Binance Smart Chain. Whether you are trying to expand the token portfolio or to explore the trade of categories, it is certainly worth considering WalletConnect.
Futures, Peer-to-Peer Trading, Non-Fungible Asset
“A child’s navigation west of the crypto currency: guide for cryptocurrencies, future and P2P trading in era of NFTS”
**
The world of the crypto currency exploded into a huge and complex landscape, and more players are fighting for dominance on the market. Basically, the Crypto currency is designed to trade a peer between individuals holding or transmitted digital assets, such as cryptocurrencies, token and other decentralized securities. In this article, we will investigate the various types of contracts that govern these trade: Crypto Futures, Peer-to-Peer Tradition and the non-stunning (NFTS).
CRYPTO Futures
Crypto futures contracts are for delivery of a certain amount of fundamental assets, such as Bitcoin or Ethereum, at a predetermined price of a particular date in the future. These contracts are traded on a regulated exchange, such as CME (Chicago Mercantile Exchange) Bitcoin Futures, and offer traders that affect increasing their potential gains. Crypto Futures provides an effective way to invest the institutional investors and individuals of high values in the crypto currency with a lower minimum investment threshold from traditional trade platforms.
Peter trading
Reference trading peers to direct asset exchange between individuals without passing through a centralized exchange or broker. This type of trading is facilitated by specialized platforms, such as Robinhood (for shares) and Etoro (for cryptocurrency currency), which allow users to buy property and sell property with each other. Trafficking in peers removes mediators, reducing costs and increasing liquidity. However, it also introduces new risks, such as potential losses due to the volatility of the market or manipulation.
necessary assets (NFTS)
Non -bothering assets are unique digital items that cannot be replaced for their identical colleagues. NFTs are often used to present ownership of digital art, collector and other unique digital content. Unlike the CRIPTO currency, which can be easily transferred from one address to another, NFTS requires a separate record of blockchain to check ownership. This feature makes them safer and more valuable than traditional property.
Complexity Navigation
Although the Crypto currency has crossed the long way in recent years, the movement in markets that have been challenging due to factors such as regulatory uncertainty, the volatility of the market and intense competition. In order to succeed in this space, traders must be informed about market trends, implying the terminology of the contract and adapt to changing regulations. In addition, establishing trust between the parties is crucial to successfully trading peers.
In conclusion, cryptocurrency, cryptocurrency of the future, and the non-stunning that represent quickly developing the landscape of decentralized securities. Since the market is still maturing, it is crucial that merchants remain awake, informed and adaptable to navigation on these complex contracts. By understanding the unique characteristics of each asset class, traders can make informed decisions and increase their chances of success in this child west of the crypto -val.
A statement of the renunciation of responsibility:
This article is only for informative purposes and should not be considered as an investment advice. Cryptocurrency markets are very speculative and have inherent risks. Always conduct a thorough research before investing in any property.